Cerber3 ransomware, ways to remove it and ways to protect the data.
Today we
talk about a virus called Cerber3. It appeared on the expanses of the Internet
recently, but thanks to its big names and high performance has become one of
most dangerous ransomware. This virus has a high code quality, a lack of vulnerabilities
and complex encryption. In addition, the virus has been created by experienced
developers who take into account the errors in previous versions, and is now
going to make us all sweat, decoding it.
What is
Cerber ransomware family
Viruses from
Cerber family are characterized by their high efficiency and complexity. Cerber
virus #1 had appeared in the Network about a year ago, and immediately became
the most dangerous, infecting tens of thousands of computers and giving hackers
an opportunity to earn hundreds of thousands of dollars. Since Cerber viruses
use a complex asymmetric encryption algorithm is the AES, decryption is
practically impossible, and the only way to deal with the virus - to crack the
code, or hack hacker’s site that stores encryption keys. This process requires
a lot of time and effort, and the very first Cerber virus was the most
successful, took several months of work. Cerber2 version was considerably
weaker, and its hacking took less than two weeks. We cannot predict how long it
will take Cerber3 hacking the code, but we hope that this will happen as soon
as possible.
How Cerber3
works
According
to its method of operation Cerber3 is no different from any other ransomware.
It penetrates to the computer via trojans, through torrents or via e-mail
spamming. If the user often uses free software or pirated media content, he
becomes easy prey for many viruses. Security can be only achieved by acquiring
licensed content on the official websites. But how to protect yourself from
viruses, penetrating to a PC via e-mail? You can do this by making sure that
any emails you open are safe. Ransomware use simple penetration scheme: they
sent a letter to the user, which should be of interest to him. Naturally, the
most user’s interest is the material gain, and hackers know it. The user
receives a letter that he has a package waiting in the mail office, but as a
result of an error they could not send it to him. User needs to download the
documents attached to the letter, fill it in and send to the address for the
parcel. Of course, anyone would be happy to receive the parcel, the existence
of which he had not even suspected. However, an attachment contains a virus,
and if a user opens it - the computer will be infected immediately.
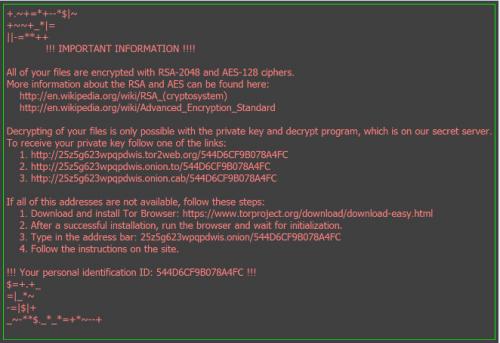
When the
user opens the message, the setup file enters the system and begins its work
immediately. The virus shows no signs of life until all the data on the user's
computer will be encrypted, and only after that - sends a message with ransom
demands. The user receives a message, which indicates the virus configuration
and website address for payment. Also, the virus changes the desktop wallpaper
and all the encrypted files are assigned to an extension .cerber3. After that,
you have only one way to recover the data for free - with the help of backups.
In addition to backups, there are other ways of recovery, but they cannot
guarantee you success, since most viruses have learned to completely delete
files from your computer, or close access to them.
How to remove
Cerber3
As long as
we cannot provide a working method of data decryption, if you do not want to
pay hackers - you need to remove the virus from your computer, and wait until
the software decryption will be released. The virus must be removed in order to
be able to continue to use the computer without compromising files. Removal can
be done manually or by means of special anti-virus program. If you need help in
removing Cerber3, or want to learn more about ransomware and the ways to defend
your data from it - you should read the extended article about how to remove Cerber3 with detailed instructions and
videoguides.
Post Your Ad Here
Comments